Amazon.com: Uncanny Coincidence: Book 9 in the Jerry McNeal series (A Paranormal Snapshot): 9781951386269: Burton, Sherry A.: Books

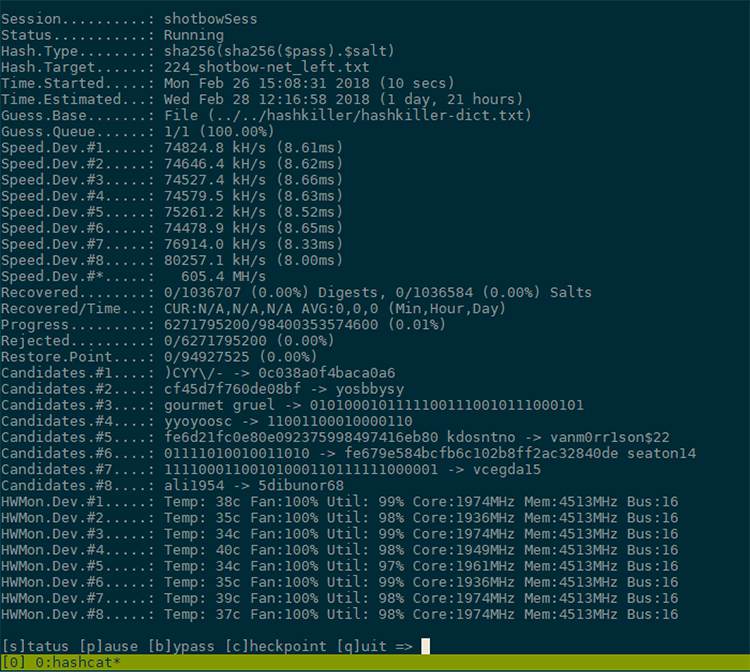
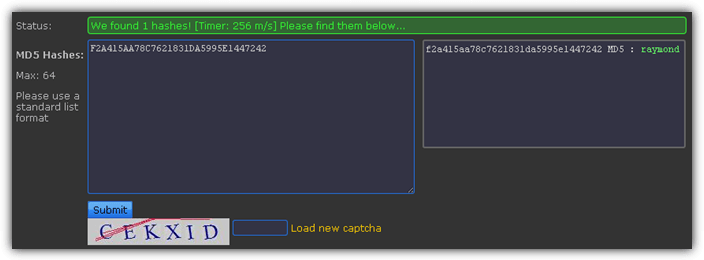
Password hacking / password cracking – www.hashkiller.co.uk | University of South Wales: Cyber University of the year: Three years running: 2019, 2020, 2021

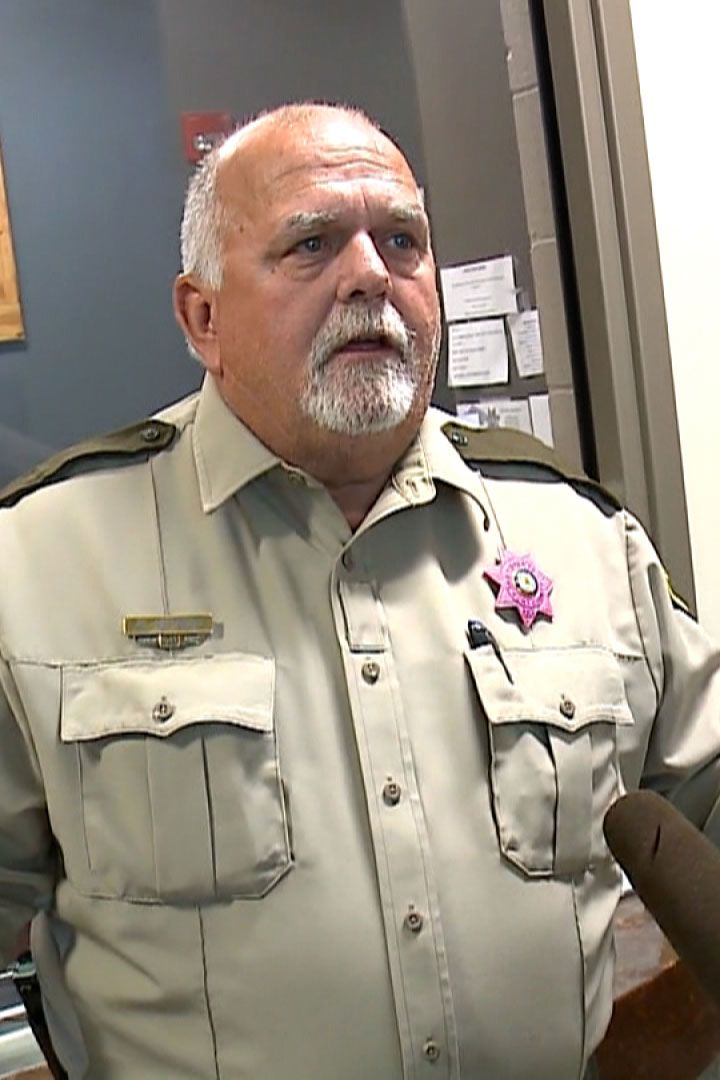
Accused killer pit two in fight before choking, torturing WL woman found near Kentland, court doc says

Fax Tree Killer Men's Tee, Graphic Tees, Funny T shirts for Men - Black MH200FUN S13 4XL - Walmart.com






![Hashkiller - Kali Linux - An Ethical Hacker's Cookbook [Book] Hashkiller - Kali Linux - An Ethical Hacker's Cookbook [Book]](https://www.oreilly.com/api/v2/epubs/9781787121829/files/assets/714fa5ac-a3a0-4378-b325-97dee1e71141.png)